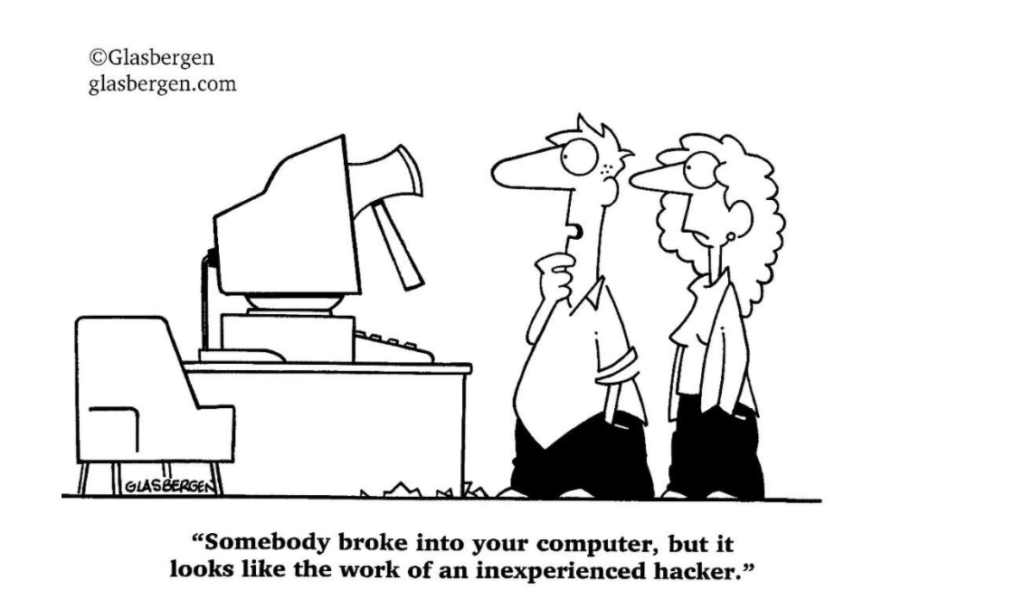
Or Is It As Easy To Get Into Your Computer System As It Is To Open A Bag Of Cement With A Trowel?”
Words: Artie Bernaducci
Photo: Glasberg
When we talk about you retiring someday, it is not just about finances. It is also about protecting what you have and that includes your personal and business identity.
Hardly a day goes by anymore without some sort of cyber breach being reported on the news.
The U.S. Government, Target, Home Depot, Anthem, and even Equifax are just a few of the more noteworthy attacks. But, while large companies and entities that hold the personal and financial information of millions (or even just thousands) of consumers may be extremely enticing to cybercriminals, the reality is small companies are also highly attractive... In many cases, they may even be more at risk for a data breach.
There are numerous reasons for this — starting with the fact that many small businesses don’t have the proper security systems in place. Having too little security, or the wrong type could lull you into a false and dangerous sense of security.
There is an education gap too because people do not realize they are a victim of identity theft until they make a large purchase like a house or a car and issues show up on their credit report.
When someone steals your personal or business information and uses it, it can cause havoc with your finances, reputation, and credit history. Resolving it can take a lot of time and money, neither of which you want to spend. All that said, please know that even if we do ALL the best practices in the world, we can still get hacked!
So, it is a necessary thing to consider having because it buys us TIME to minimize the damage. Best practices can let you know days, weeks, months, and even years in advance of something happening, or if something does happen, it can prevent it from growing into a much bigger threat.
After being hacked in 2004 I needed to know HOW I was hacked and HOW I could protect myself against it as much as possible. Becoming an avid student, I put a book together that is on Amazon called:
“What Every Person and Business Owner Ought to Know About Identity Theft: Before it Happens”.
It evolved out of clients asking for my guidance in this area enough times that it became a part of my practice. The book discusses best practices for the individual and the business owner.
Dispelling Online Security Myths
Although you may feel that you aren’t a prime target for a cyber-attack, the reality is that anyone and any company can become a victim – and in many cases, individuals and businesses already have been affected, even if they don’t yet realize it. While this false sense of security may seem comfortable, it can put you and your business in a very vulnerable position. For example, less protection means that cybercriminals can more easily get to, compromise, and possibly even hold ransom your company’s private data (along with that of your employees and your customers).
It can also mean that you are less prepared if an attack occurs. Here, in addition to retrieval of your and your company’s information, there is a long list of costly and time-consuming criteria that could be required just to get you back to square one. Your company could also be at risk of lawsuits from those whose information has been compromised.
Depending on the situation, the expenses could be staggering – and in some instances, due to the expense, the loss of goodwill, and ultimately the loss of customers, it can even drive a company out of business. With that in mind, it is essential to dispel some of the most common myths regarding online security. These include:
“My Company is Too Small to Be a Viable Target for Cyber Criminals”
You may feel that, because the Internet is such a massive place, your small business wouldn’t be a viable target for a cyber-criminal. Nothing, however, could be further from the truth. In fact, in many ways, smaller companies are even more at risk than larger ones. One reason for this is because many small businesses just simply don’t have the massive security budget that larger companies have.
Therefore, their systems are much more at risk. Through the use of various automated tools, cybercriminals can probe systems to find more vulnerable networks and computers – and oftentimes, these activities can go undetected for weeks, months, or even longer. This gives hackers plenty of time to access what they need before anyone even notices.
“My Company Has Anti-Virus Software and/or a Firewall in Place”
While anti-virus software can be a good first step in online security, it is only a small part of a good, solid overall security plan. Using a previous analogy, think about it this way – although you may have built an 8 ft. tall block wall around your backyard, do you rest easy at night feeling that your home is 100% protected from an intruder?
If that intruder wants to climb over it, he will. And if a hacker wants to get to your data, he will too!
“My Employees and I Don’t Access Unsafe Web Locations”
Not accessing unsafe websites and/or other unsafe online locations is another big myth that could lull you into a false sense of online security. One of the biggest reasons for this is because cybercriminals can attack in any number of other ways, such as through phishing emails that contain unsafe links or attachments.
Oftentimes, these emails may appear to come from reputable sources, such as a financial institution that you do business with — which can trick even the savviest Internet user into clicking a link that is infected with malware. Also, while you may feel that you can trust your employees not to visit unsafe websites or to click on unknown links, that may not always be the case.
“I Will Surely Notice If My Company is Attacked”
In the past, you may have been able to notice if your system had been compromised. That is because computers would often start to run slow, and pop-ups would appear on the screen.
Today, however, cybercriminals are much more astute and efficient. The malware that is used in more recent cyber-attacks is typically undetectable and is designed to evade normal detection systems.
Having a Backup Plan in Place
It is important to go over backing up your company’s (and your personal) data – just in case of a cyber-attack. Even if you are busy, running late to a meeting, or trying to finish creating a big presentation, making sure that your data is securely backed up can be worth much more than you might think.
That is because data loss can have a multitude of consequences – none of which are good. Losing your important information can be the result of a hacker – or even a real-life criminal who gets hold of a laptop or smartphone that contains company trade secrets, customer data, and/or any number of other pieces of information.
In addition to that, accidents can happen, too – such as a glass of water spilling on your or one of your employees’ computers – which can also result in the loss of key data to you and your business. In any case, you must have a backup plan for your data.
What exactly is a data backup plan?
In its most basic sense, it entails making copies of your data, which are then stored someplace safe, so that information may be restored in case anything should happen to the current device. You can back up your data in any number of ways, including via an external hard drive and/or through the cloud. Many experts agree that you should have at least three copies of your data and that these backups be kept on different types of support.
So as not to forget about making a data backup, it can be helpful to maintain a consistent schedule of backing it up regularly. For example, every Friday at noon, or even every day at a certain time. Concerning company or business-specific data, it is always a good idea to keep your data backups in a secure, offsite location. And, just as in other areas of the online world, be sure that you secure your data backups with very strong passwords – and that the passwords are also kept safe.
For more information on identity theft protection for your masonry business and yourself, there’s a lot of great information at www.BizIDProtection.com.